Torrenting in 2025:
The Privacy Landscape, Leak Paths, and What Actually Matters
Torrent activity keeps evolving, and with it the privacy risks. This guide explains what's changing in 2025 — across clients, protocols, trackers, blocks, and common leak paths — so you can make informed, safer choices without hype.

🌐 What "torrenting in 2025" actually means
Torrenting today is not just a client and a .torrent file. It's an ecosystem — public and private trackers, distributed discovery via DHT and PEX, various transport options, evolving client defaults, and a patchwork of ISP and CDN-level interventions. Users run torrents on desktops, seedboxes, NAS devices, and headless servers — each with a different risk profile.
📈 Three trends driving user behavior
📡 Protocol behavior and your exposure surface
BitTorrent is efficient because it's open: peers discover each other rapidly and connect directly. That openness is also why your endpoint can be seen by many peers if your configuration allows it.
⚙ How client defaults and settings affect privacy
Modern clients are far safer than they were, but defaults can't account for every network topology. A few areas to inspect:
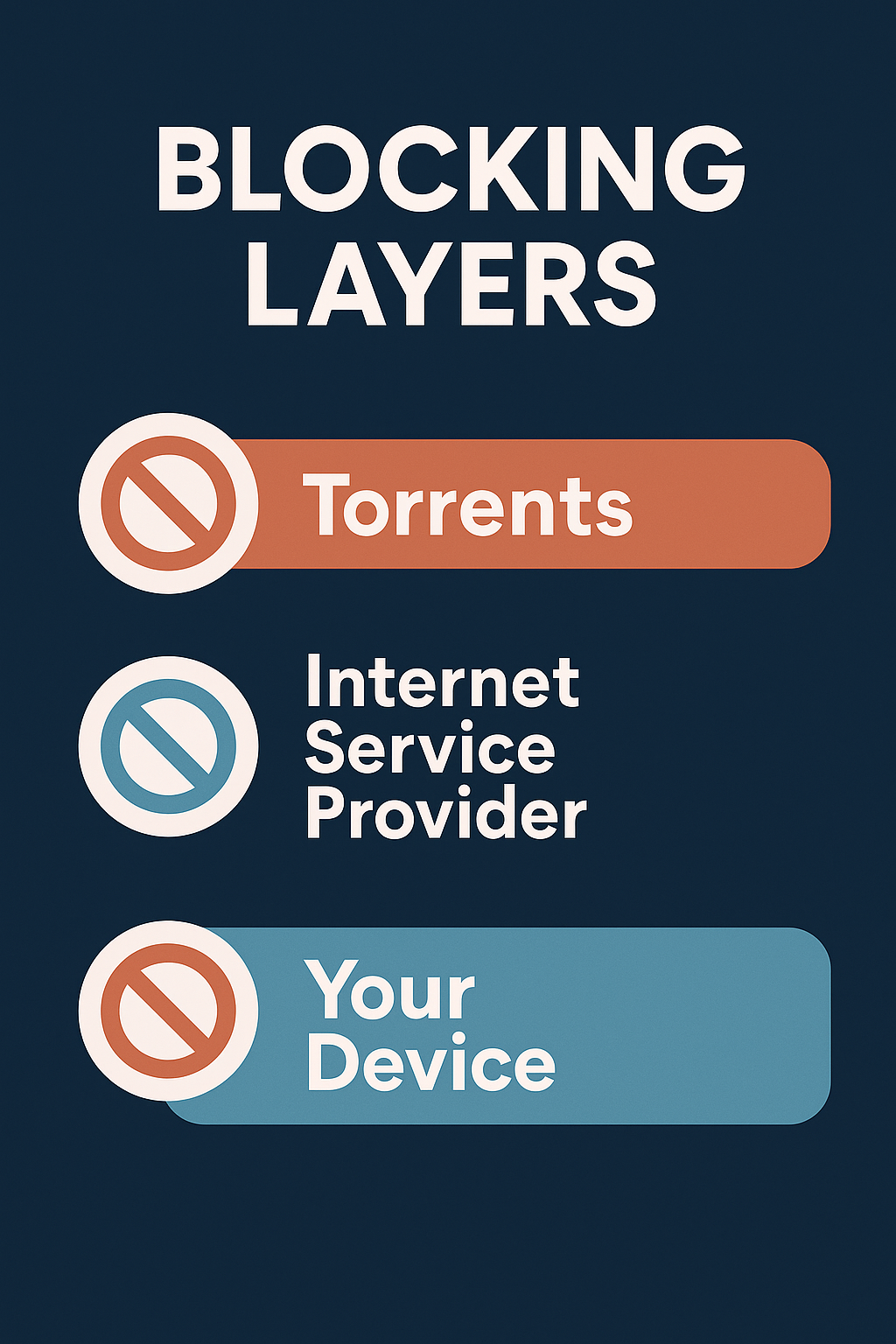
🧱 Blocking and disruptions: what users actually experience
💧 Common leak paths — and how they happen
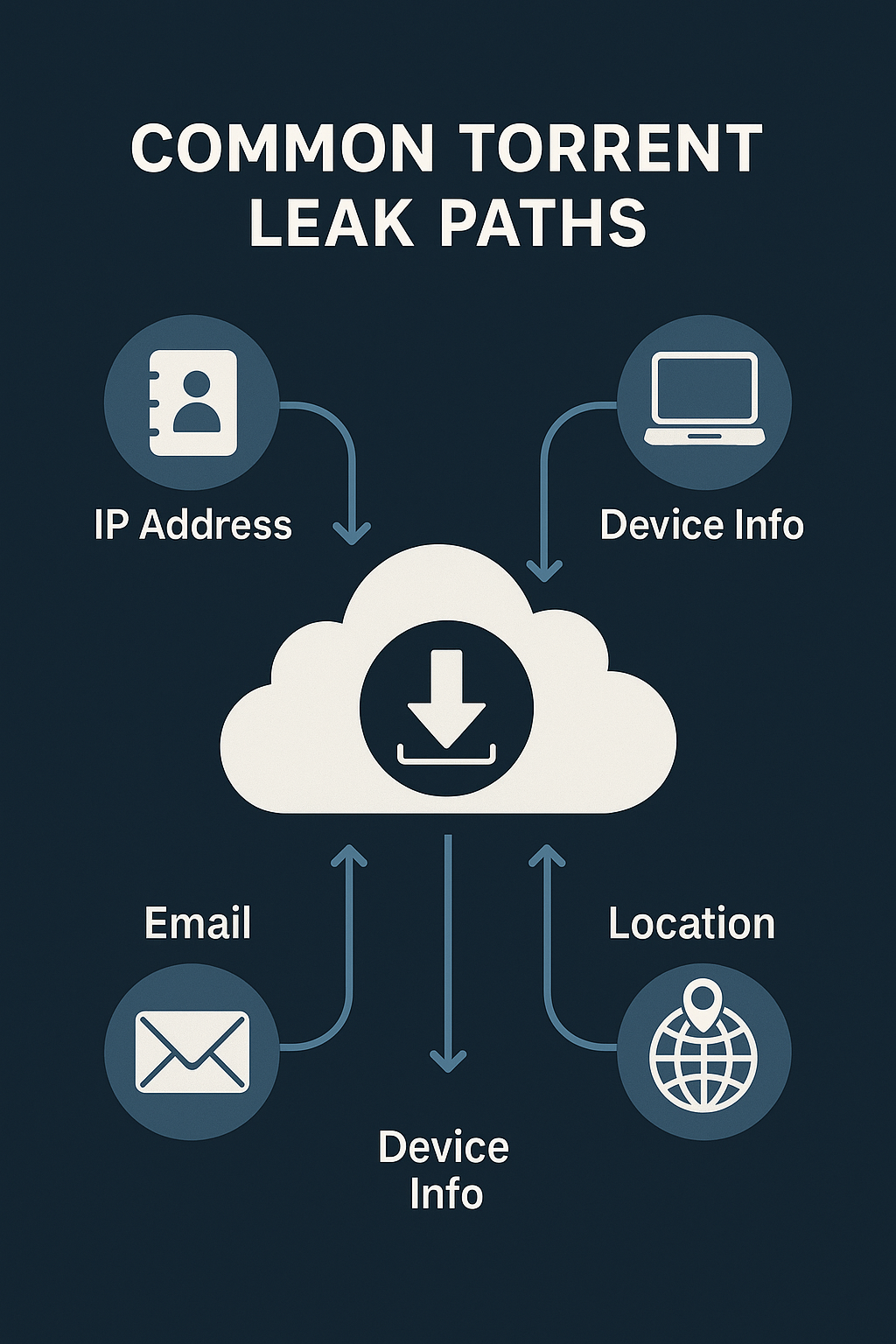
Client restarts while tunnel isn't ready
OS boot → VPN/proxy not fully initialized → client autostarts → brief connections via default route. Fix by delaying autostart or enforcing firewall rules that deny egress unless the trusted interface is up.
Web UI exposure
A web UI forwarded to the internet without auth or IP restrictions is a significant attack surface. Use strong credentials, unique ports, and a reverse proxy with rate limits and allowlists.
Browser overlap (WebRTC, extensions, profiles)
A browser session with WebRTC enabled can reveal routes separate from your torrent client. Keep separate browser profiles and disable or restrict WebRTC if your model requires it.
DNS inconsistency
OS or router DNS may not match your intended resolver policies, especially after sleep/resume or adapter changes. Confirm resolver behavior after every network transition.
⚖ Public, private, or trackers-only?
| Approach | Pros | Cons | Best for |
|---|---|---|---|
| Public + DHT/PEX | Fast peer discovery, broad availability | Wider exposure; more fakes | General users prioritizing speed |
| Private + limited DHT/PEX | Curated releases; community accountability | Rules, ratios, account data exists | Users wanting quality and community |
| Trackers only (no DHT/PEX) | More controlled discovery | Slower peer growth; needs good trackers | Strict threat models |
FAQ Frequently asked questions
Does encryption alone make me anonymous?
Is DHT unsafe by default?
Are private trackers "safe"?
What about seedboxes or headless servers?
Free torrent IP check — no signup
See exactly which IP the swarm observes from your client — the fastest way to know if your privacy layer is working.
