Stop Configuring SOCKS5 Manually —
Auto-Config Does It in One Click
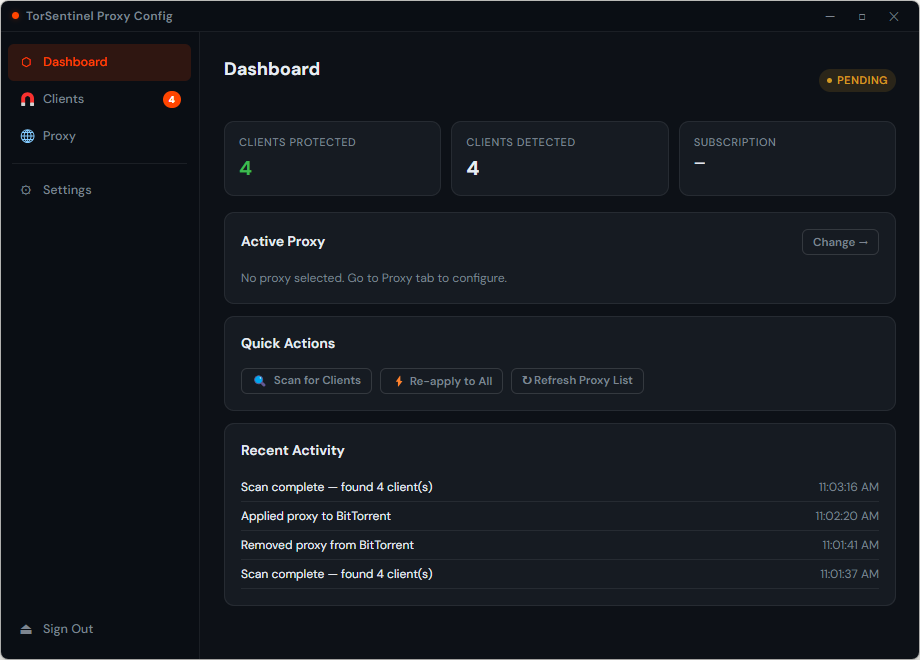
Manually editing proxy settings in every torrent client is tedious, error-prone, and easy to forget after an app update resets your config. The TorSentinel Proxy Auto-Config app scans your PC, finds every installed torrent client, and injects the correct SOCKS5 credentials automatically — no config files, no copy-pasting, no mistakes. Sign in with your Armor account for instant zero-config setup, or use manual mode to configure any SOCKS5 provider you already use.
- ✓ Windows 10 or 11
- ✓ At least one torrent client installed (qBittorrent, µTorrent, BitTorrent, Vuze, etc.)
- ✓ A TorSentinel Armor subscription (for automatic credential setup) — or any other SOCKS5 proxy credentials for manual mode
- ✓ About 2 minutes
? Why not just configure the proxy manually?
You can — and our other guides cover exactly that for qBittorrent, uTorrent, Transmission and more. But manual configuration has real failure modes:
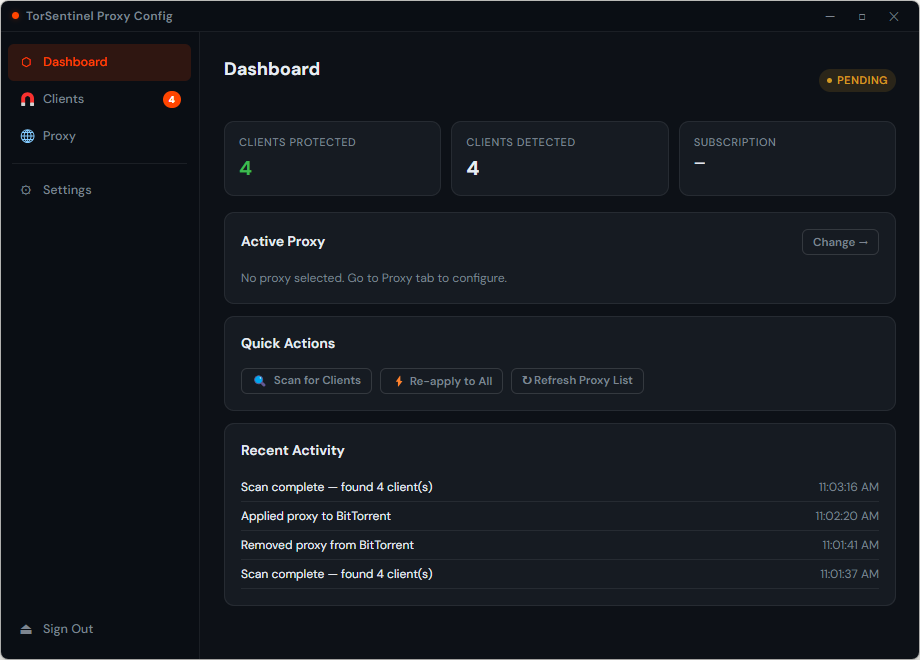
The Auto-Config app eliminates all of these. It reads your Armor credentials once, scans for every installed client, and writes the correct config — every time, with zero opportunity for human error.
Download, install, and choose your mode
After installing the app you're presented with two paths. Choose the one that matches your setup:
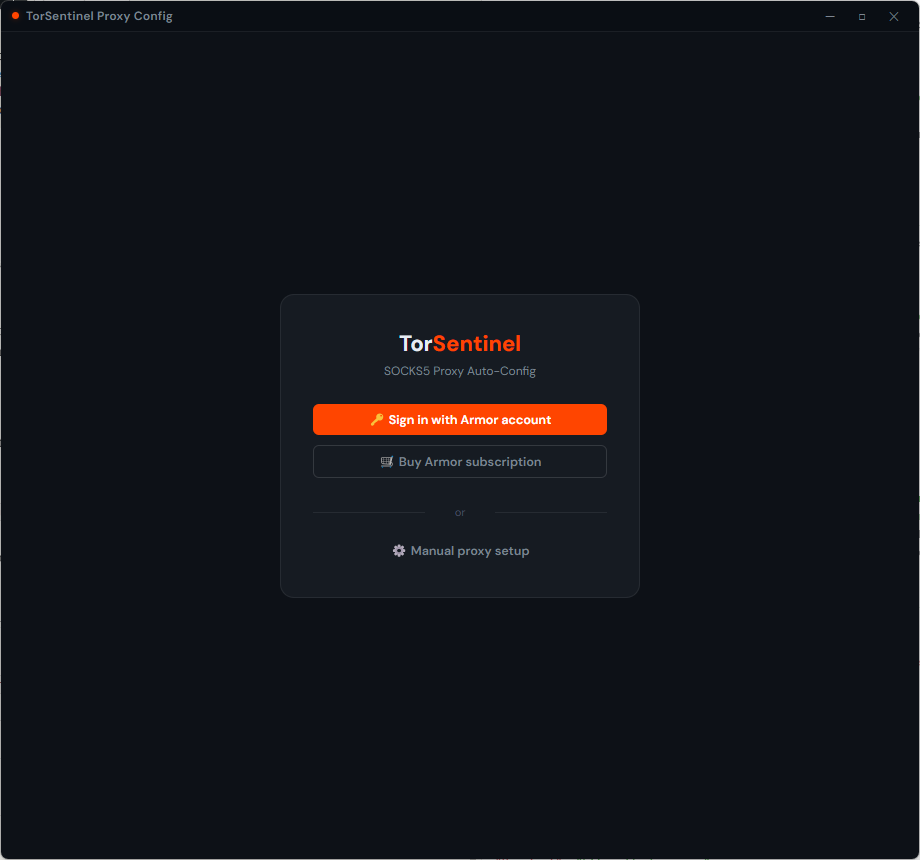
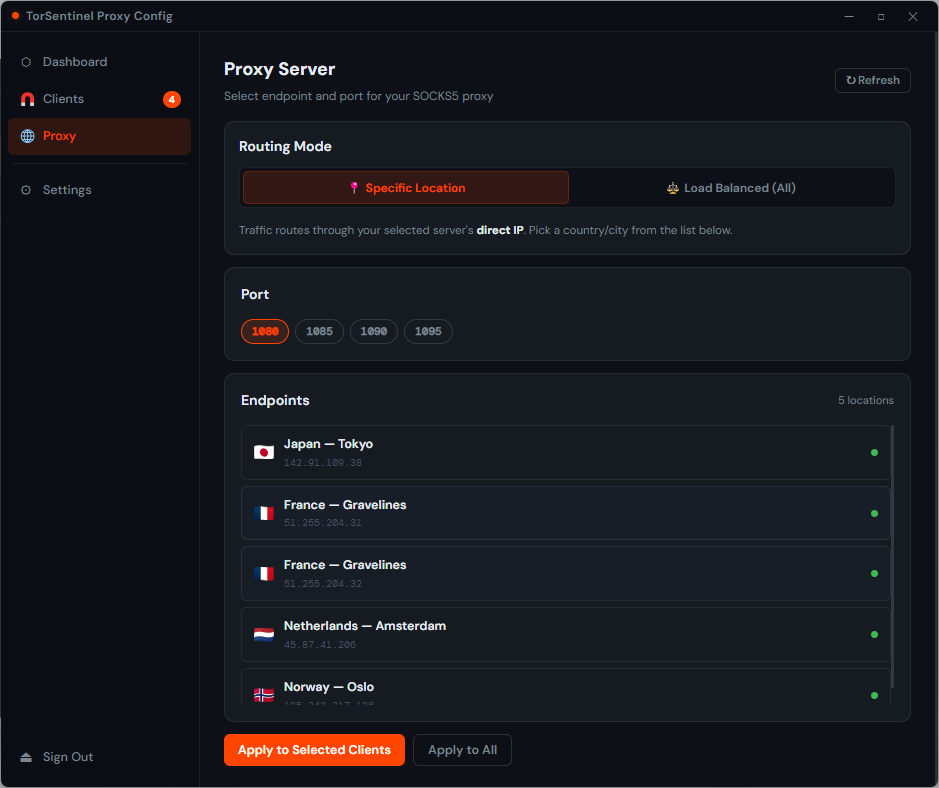
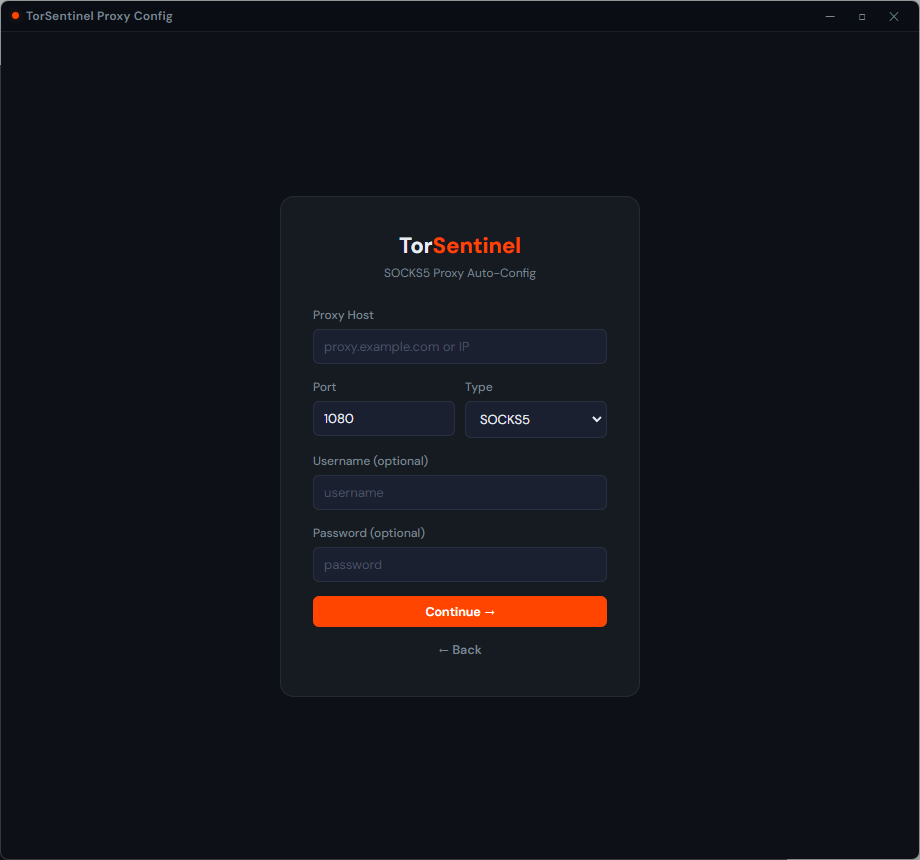
Enter your proxy credentials
Armor mode: after signing in, your server, port and credentials are filled in automatically. Just pick a location and you're done. Manual mode: enter your proxy host, port (default 1080), proxy type (SOCKS5), and optionally a username and password for authenticated proxies.
Using a different provider (Mullvad, AirVPN, iVPN, your own server)? Click Manual proxy setup on the launch screen. Enter your proxy host, port, type, and credentials — then proceed exactly the same way to scan and apply.
Click "Scan for Clients"
Switch to the Clients tab and click Scan for Clients. The app searches common install paths and registry entries for every supported torrent client. Each detected app appears in the list with its config file path and current proxy status.

Click "Apply to All" — done
Click Apply to All to push the SOCKS5 config to every detected client at once, or select individual clients if you only want to protect specific ones. Each row turns green with a PROTECTED badge the moment the config is written successfully.
Verify the proxy is actually working
Configuring the proxy and having it work are two different things. Run a live leak test to confirm your torrent traffic is actually going through the proxy and not exposing your real IP.
✓ What successful protection looks like
💡 Tips for keeping your protection current
FAQ Troubleshooting
My client isn't appearing in the scan results
The app shows PROTECTED but the leak test still shows my real IP
Windows SmartScreen blocks the installer
Can I use this with a provider other than TorSentinel?
Get Armor — Unlock the Auto-Config App
Armor gives you the SOCKS5 gateway credentials, the Auto-Config desktop app, the WireGuard VPN app with port forwarding, and 24/7 realtime leak monitoring — all in one plan.
