SOCKS5 Proxies vs VPNs:
Speed, Control, and Privacy in 2025
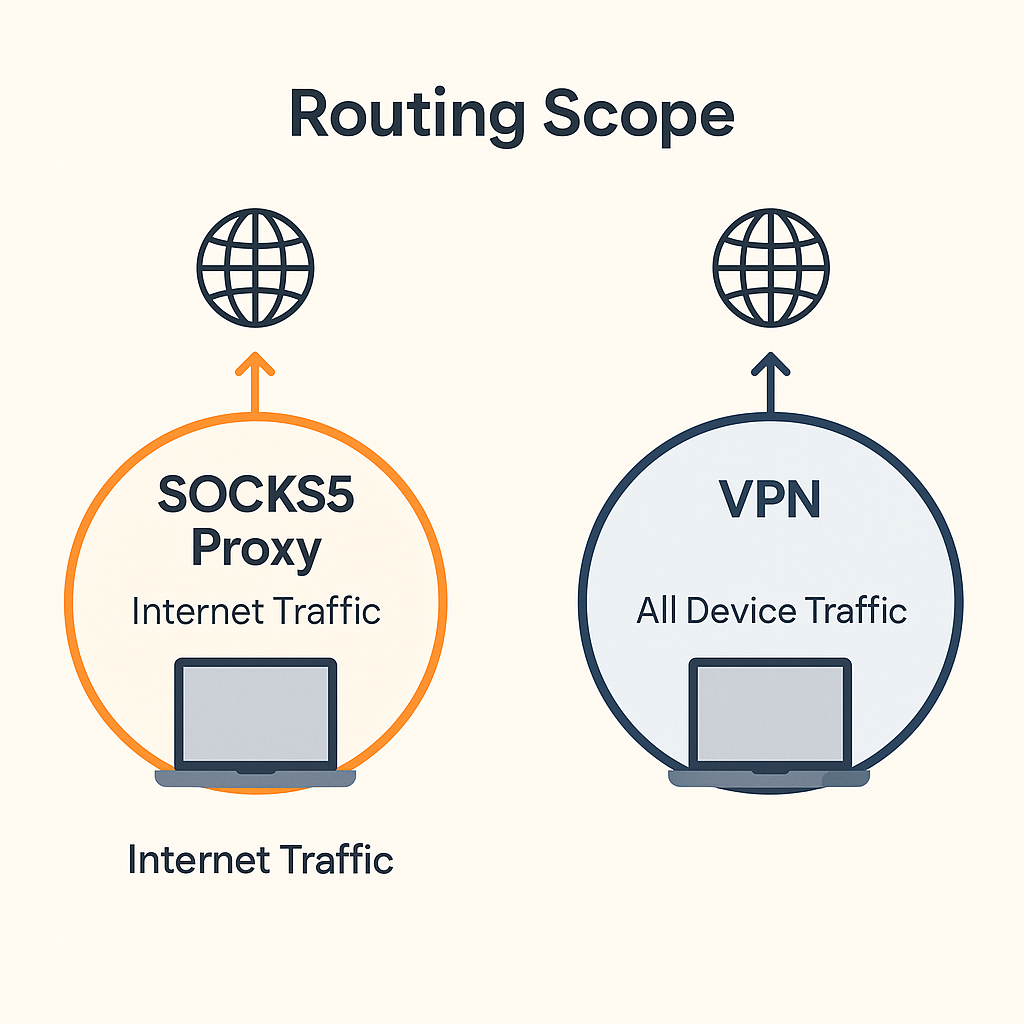
SOCKS5 and VPNs both route traffic through a trusted path, but they operate at different layers. SOCKS5 acts at the socket level per application, while a VPN creates a system-wide tunnel. This guide breaks down the tradeoffs so you can choose the right tool — or combine both effectively.
≡ Quick definitions
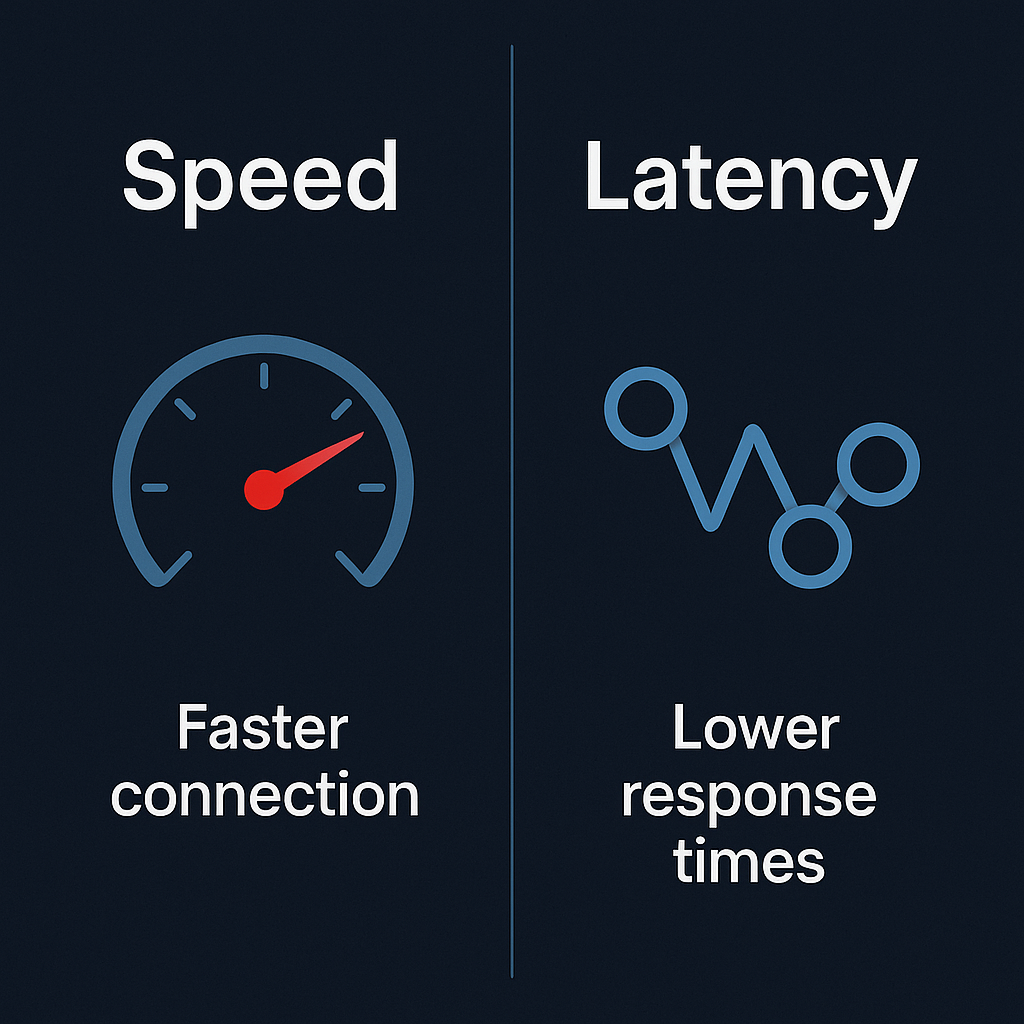
App connects to a proxy that opens the destination connection on its behalf. Supports TCP and UDP. No encryption by default — excellent for precise per-app routing and performance.
System or user-session traffic is encapsulated into an encrypted tunnel. Simple for total device coverage. Adds some overhead compared to a targeted SOCKS5 route.
⚡ Performance and control
🛡 Privacy model and leak prevention
⚖ When to choose SOCKS5, when to choose a VPN
| Use case | SOCKS5 | VPN |
|---|---|---|
| Single app needs routing + speed | ✓ Excellent — low overhead per-app route | Possible but heavier than needed |
| Whole device privacy policy | Can work but requires many app rules | ✓ Strong fit — one tunnel for all traffic |
| Containers or headless services | ✓ Great — point service at proxy endpoint | Works if runtime is attached to tunnel |
| Strict confidentiality for every byte | Pair with app TLS or run inside a VPN | ✓ Designed for this by default |
| Torrenting with max speed | ✓ Ideal — no tunnel overhead on peers | Works but encryption adds latency |
🔍 How SOCKS5 hides your IP
With SOCKS5, the destination sees the proxy server as the source of the connection — your device IP stays hidden from the remote service. For end-to-end confidentiality, use TLS inside the application or run the app inside a VPN while still enjoying the per-app control of SOCKS5. This combination gives you the best of both: encryption from VPN, routing precision from SOCKS5.
✦ Recommended pattern: SOCKS5 plus guardrails

🛰 Where TorSentinel fits in
Free leak check — no signup
Find out what IP the swarm actually sees. If it's your real IP, Armor fixes it in minutes.
