qBittorrent IP-Leak Protection:
The Complete Hardening Guide
Most qBittorrent setups leak your real IP — even with a VPN active. Interface binding gaps, DHT announcements, and startup races all expose you. This guide closes every one of those holes.

This guide shows you how to configure qBittorrent for strong IP-leak protection without sacrificing day-to-day performance. Step-by-step instructions for home users, with deeper notes for power users running headless or seedbox setups.
Reduce the chance that your real IP appears in a swarm or a tracker due to timing gaps, misconfigurations, or UI exposure.
✔ Prerequisites
Bind qBittorrent to a trusted interface
Binding ensures qBittorrent only sends and receives traffic over your trusted adapter. If that adapter goes down, the client will not silently route over your default interface.
Tools → Options → Advanced
Scope discovery: trackers, DHT, and PEX
Peer discovery accelerates downloads but also broadens where your endpoint can appear. In Options → BitTorrent, toggle DHT and PEX to match your threat model.
Transport and ports
Web UI hygiene Critical if headless or remote
The Web UI is a frequent exposure point. Treat it like production software.
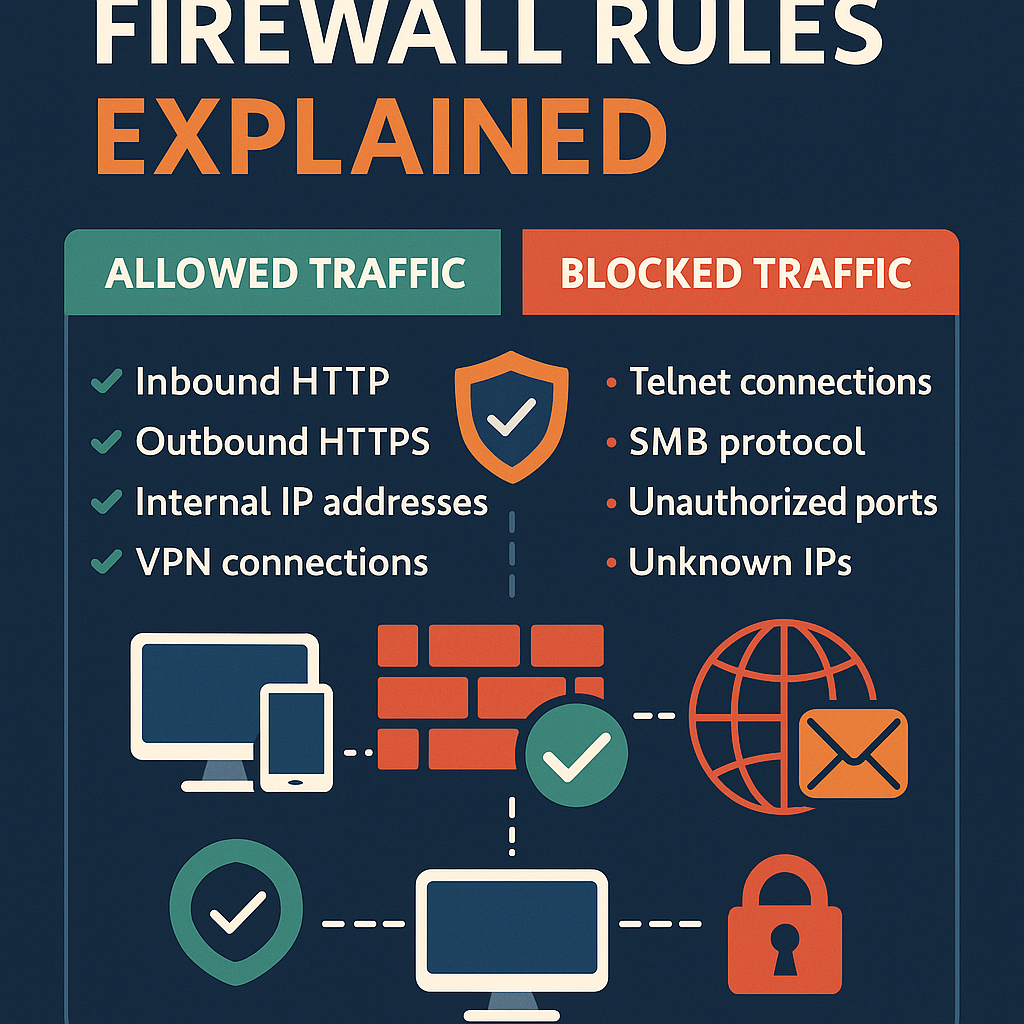
Options → Web UI, enable authentication with a strong unique password127.0.0.1 or your admin IP range) where possibleFirewall policy: deny by default outside the trusted path
Concept: Allow qBittorrent → trusted adapter. Deny qBittorrent → any other adapter. If the adapter is down, traffic fails closed.
DNS consistency and IPv6 handling
After reboots or adapter changes, resolvers may shift. Confirm that your DNS and IPv6 policies remain consistent with your intended configuration.
Safe startup and restart windows
Many leaks happen during boot: the OS starts, your tunnel or proxy isn't ready yet, and qBittorrent autostarts and briefly announces over the default route.
Private vs public trackers
📋 Minimal hardening checklist
🔧 Troubleshooting quick wins
No peers after binding?
Web UI sluggish behind a proxy?
proxy_buffering off or equivalent.
