Layered Privacy: Building a Leak-Proof Setup
with SOCKS5 and Smart DNS Routing
True privacy online depends on layers that work together rather than one single tool. SOCKS5 is the foundation that routes application traffic with precision, while smart DNS alignment and firewall guardrails complete the structure. This guide explains how to combine them into a reliable, leak-proof setup.

⚡ The privacy stack explained
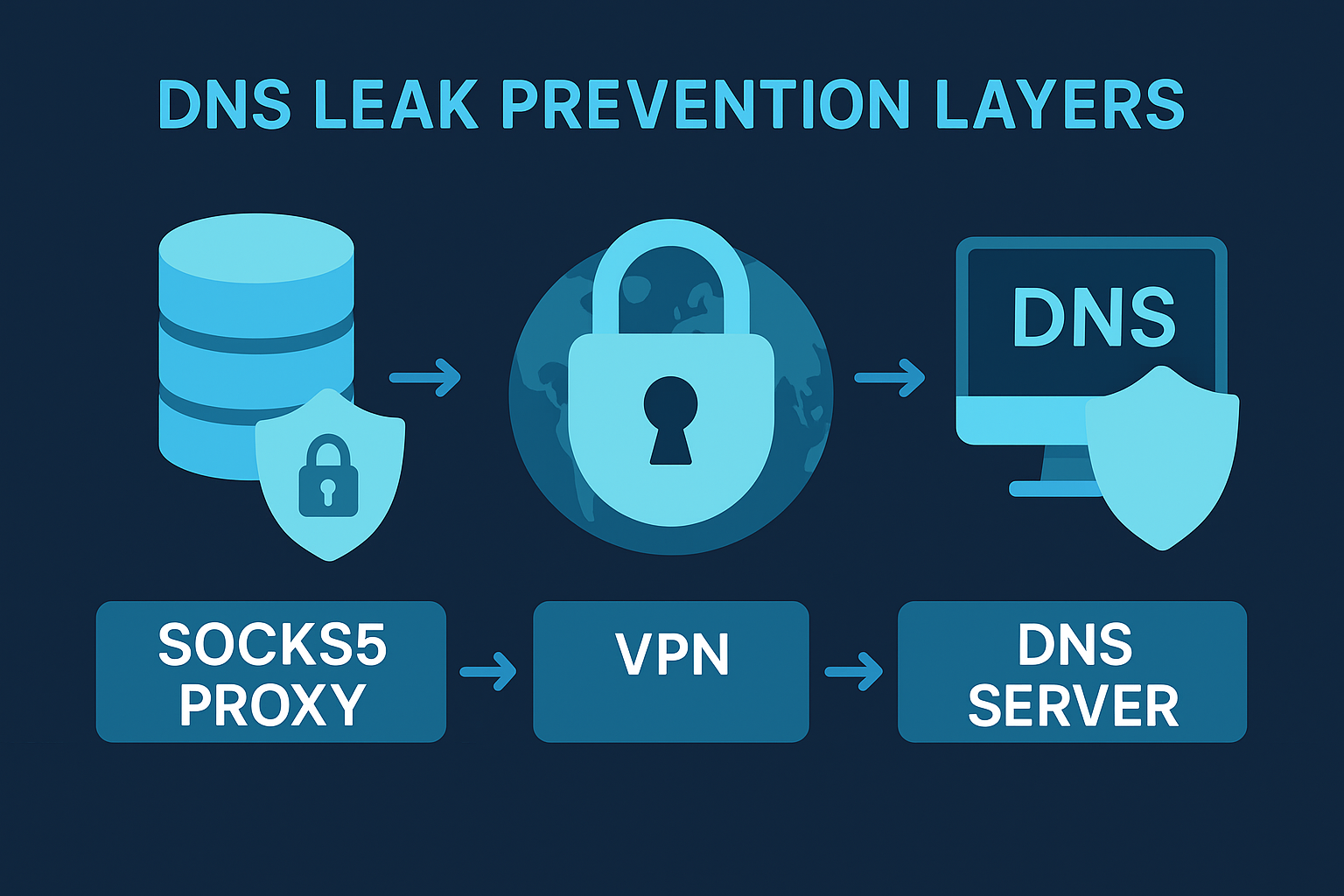
Think of your privacy setup as a multi-tier architecture. Each layer covers the gaps of the one below it. SOCKS5 handles routing and identity control, DNS manages naming privacy, and firewall rules block fallback leaks. Together, they ensure stable and predictable traffic — even after reboots or network changes.
SOCKS5 — The core layer
RoutingSmart DNS routing — The name resolver layer
DNSDNS is often the first point of failure in privacy setups. By routing DNS requests through the same SOCKS5 path — or a trusted resolver accessible only on that path — you ensure that no name lookups bypass your privacy route. A hidden IP means nothing if your queries still go to your ISP's resolver.
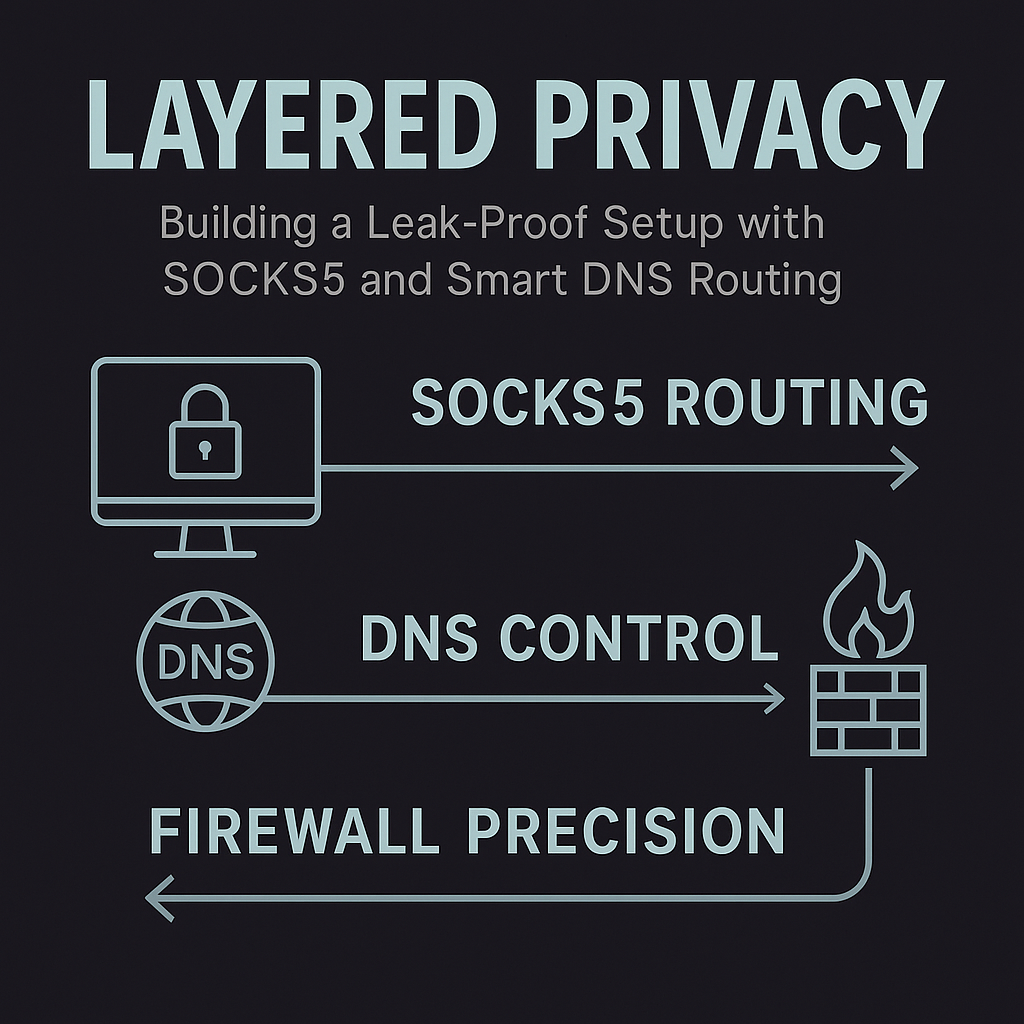
Firewall guardrails — The enforcement layer
FirewallFirewalls provide the structure that makes leaks impossible. By denying outbound traffic not bound to the SOCKS5 adapter or proxy IP, they create a fail-closed design. If the proxy disconnects, the app cannot fall back to your real IP — the alternate route is blocked entirely.
🔗 Putting it all together
⚙ Implementation steps
🛰 Monitoring the stack in real time

TorSentinel monitors adapter state, resolver identity, and proxy endpoints to detect changes instantly. This real-time feedback loop is essential for maintaining stability after reboots or network switches — situations where a previously correct setup can silently revert.
Free torrent IP check — no signup
See exactly what IP the swarm detects from your torrent client. If it's your real IP, Armor + Monitor fixes all three layers in one plan.
