Inside SOCKS5: How Smart Routing
Boosts Speed and Privacy
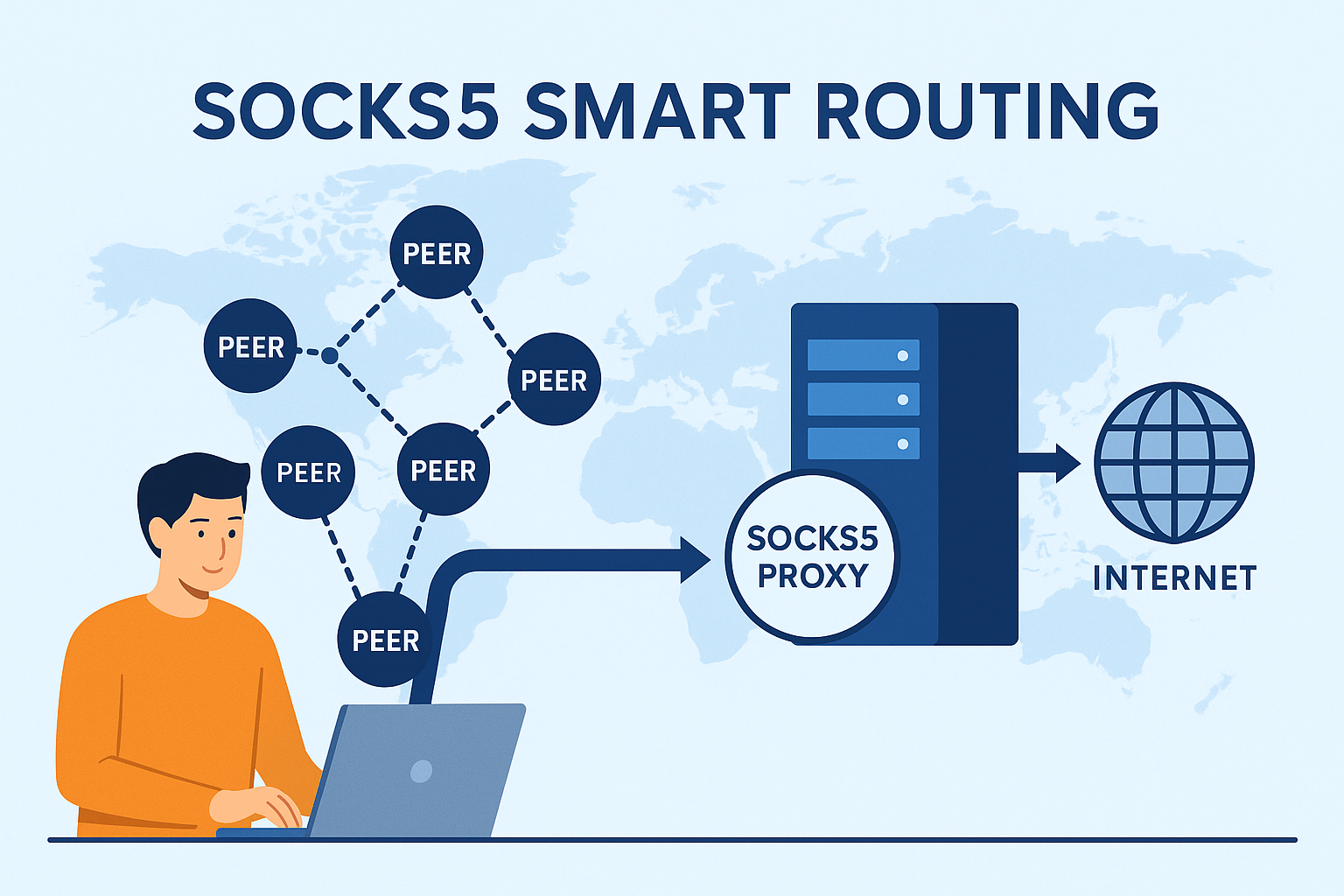
SOCKS5 is a lightweight proxy protocol that routes application traffic through an intermediate server without reshaping the whole device. Because it operates at the socket level, SOCKS5 delivers fast, predictable paths per application while keeping privacy controls simple. This deep dive explains how SOCKS5 works, why it can feel faster than a full tunnel, and the guardrails that turn speed into reliable privacy.
⚡ What SOCKS5 does and does not do
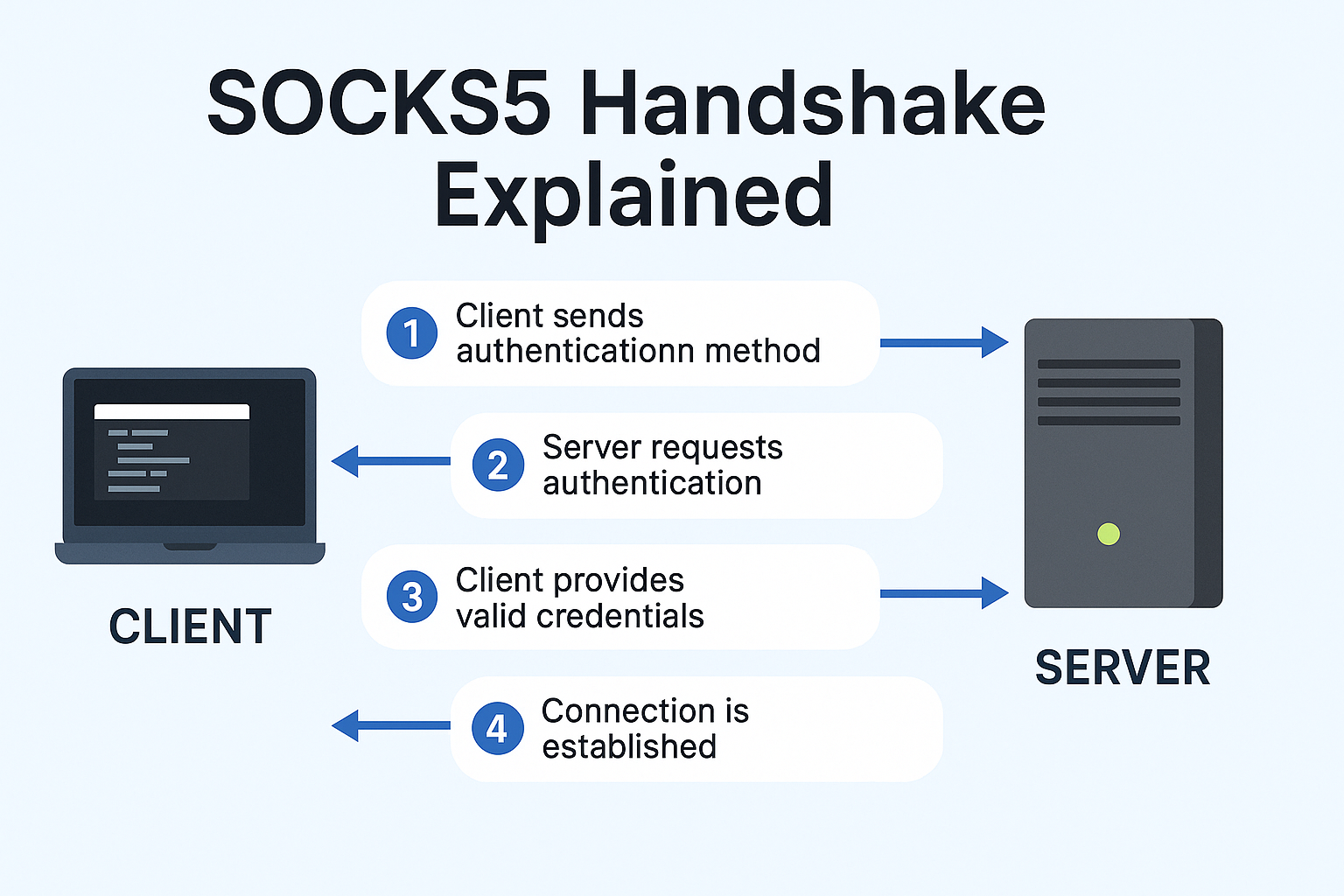
🔗 Protocol overview: greeting, auth, and commands
🚀 Why SOCKS5 can feel faster than a VPN

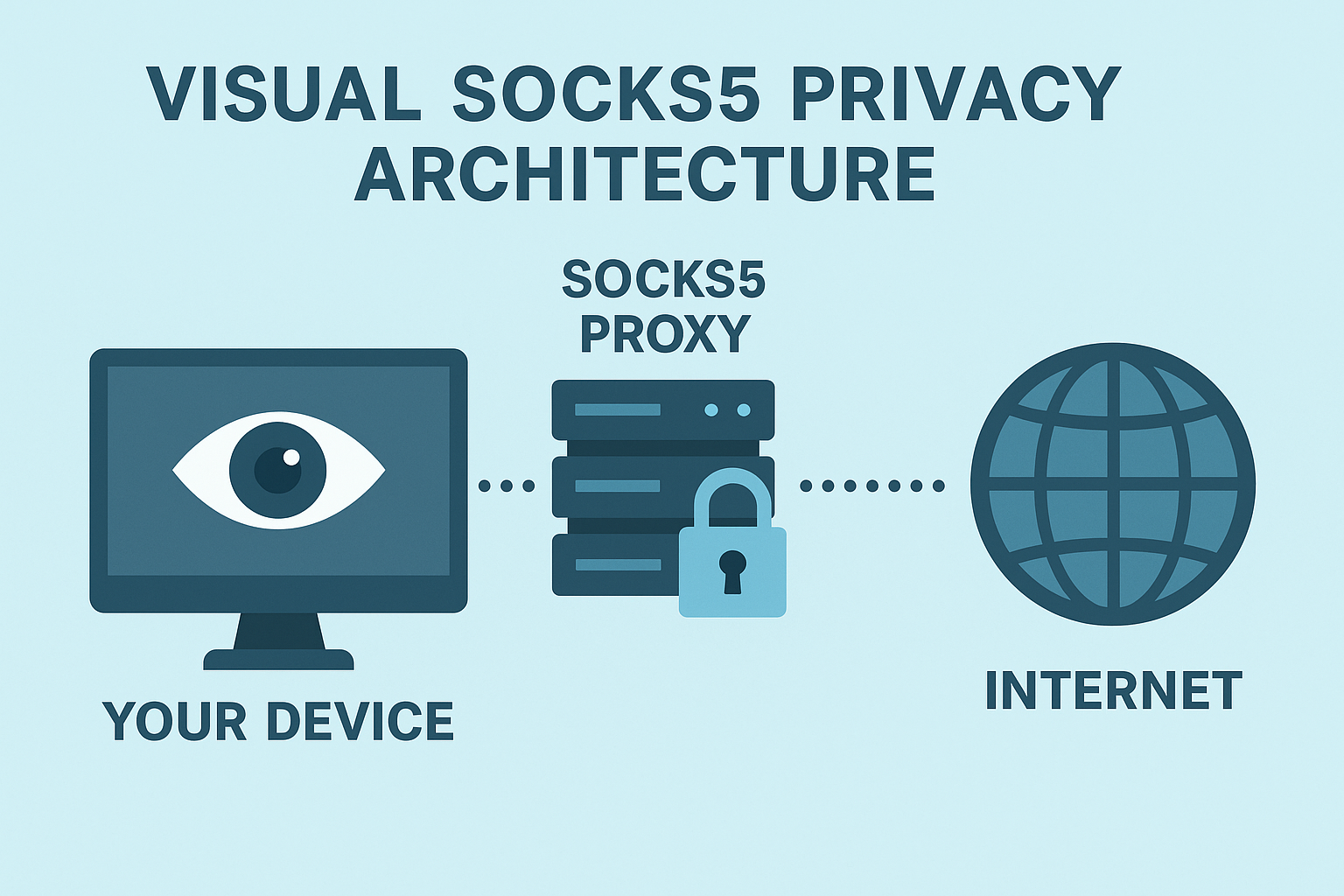
🛡 Privacy model: how SOCKS5 hides your IP
With SOCKS5, the destination sees the proxy server as the source of the connection — your device IP remains private. For strong confidentiality, add TLS at the application layer or place the app inside a VPN while keeping SOCKS5 for precise per-application routing and firewall policy.
🔍 DNS alignment and leak guardrails
Routing your traffic correctly is only half the job. DNS leaks can expose your activity even when the proxy is working. These three rules close the gap:
📡 UDP ASSOCIATE in practice
When applications need UDP, the client issues UDP ASSOCIATE and the proxy returns an address for datagrams. Application support varies — always test your specific use case and confirm that both DNS and transport follow the intended route before relying on UDP proxy for privacy.
⚙ Operational patterns that age well
✦ Recommended pattern: SOCKS5 with TorSentinel monitoring
Protect your torrent IP today
TorSentinel Armor gives you a SOCKS5 proxy tuned for torrenting plus 24/7 leak monitoring. Start your 7-day free trial — no risk.
