TorSentinel Team •
Protocol Guide
SOCKS5
VPN
Proxy
Privacy
How SOCKS5 Works:
Protocol Deep Dive, Comparisons, and Safe Configuration
SOCKS5 is a lightweight way to route application traffic through a trusted path without reshaping your entire system. This guide explains how the protocol works, when to use it, where it fits versus VPN and HTTPS proxy models, and how to configure it safely.
TorSentinel Team
·
Updated 2025
·
7 min read
·
Intermediate

⚡ What SOCKS5 does at a glance
🎯 App-level routing
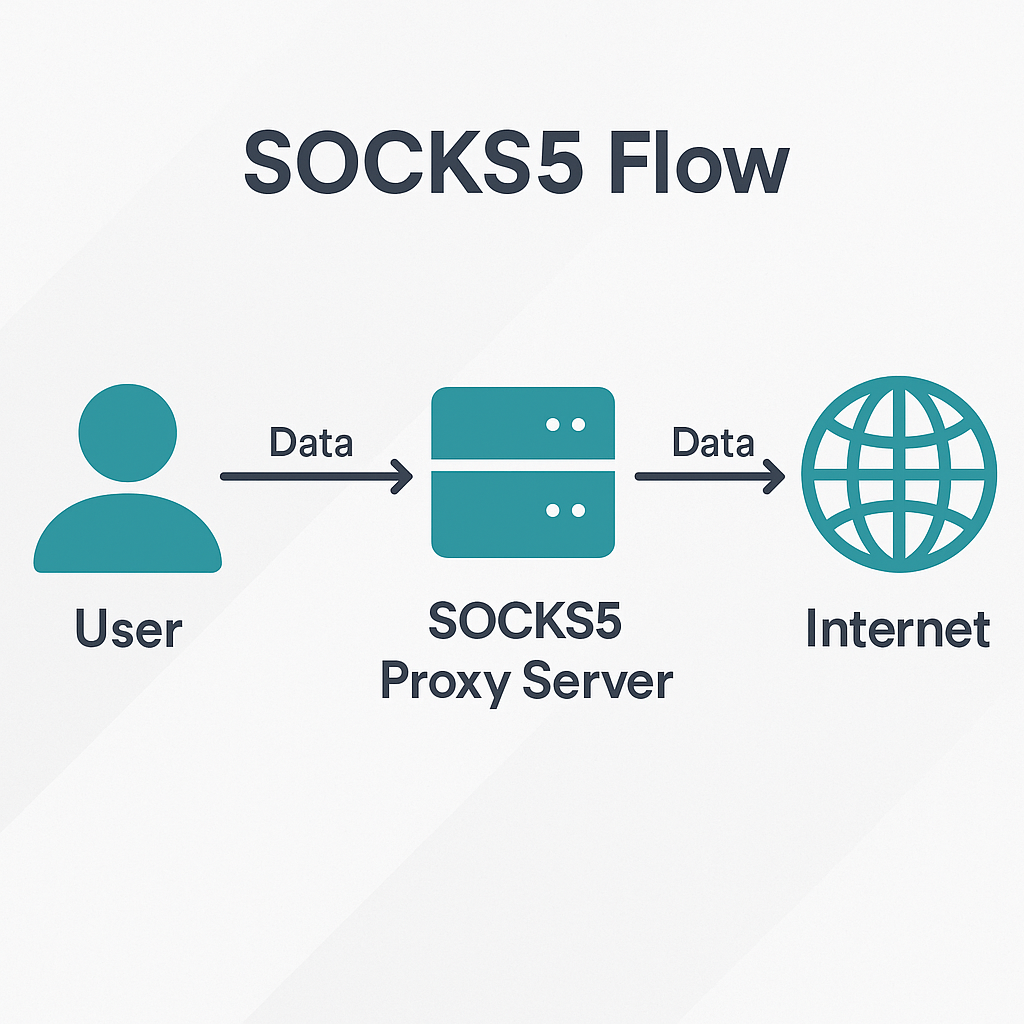
The application connects to a SOCKS5 server, which opens the final connection to the destination on its behalf.
🔓 No native encryption
SOCKS5 doesn't encrypt payloads. Most setups pair it with TLS in the app or a system VPN when confidentiality is needed.
📡 TCP and UDP
Works with TCP and supports UDP relaying via the UDP ASSOCIATE command — essential for torrent peer connections.
🔄 Protocol flow: handshake and commands
1
Greeting and authentication
The client connects to the proxy and offers its supported auth methods. The server selects one. Common options: no auth in private environments, or username + password for shared systems like TorSentinel Armor.
2
Command phase
CONNECT
Ask the proxy to open a TCP connection to
host:port and relay bytes both ways. The most common command.UDP ASSOCIATE
Ask the proxy to relay UDP datagrams. The server returns an endpoint for subsequent UDP packets — used for torrent peer traffic.
BIND
Less common. The proxy listens for an incoming connection and notifies the client when it arrives.
✦ Where SOCKS5 shines
✓
Per-app policy
Route only a single application through a controlled path without changing the rest of the system. Your browser stays on direct while your torrent client routes through the proxy.
✓
Containers and headless services
Easy to point a service or container at a proxy endpoint for clean egress control — no tunnel interface required on the host.
✓
Firewall clarity
Policies can permit the app to speak to the proxy and deny any other egress — a simple, auditable allow list rather than complex routing tables.
⚖ SOCKS5 vs VPN vs HTTPS proxy
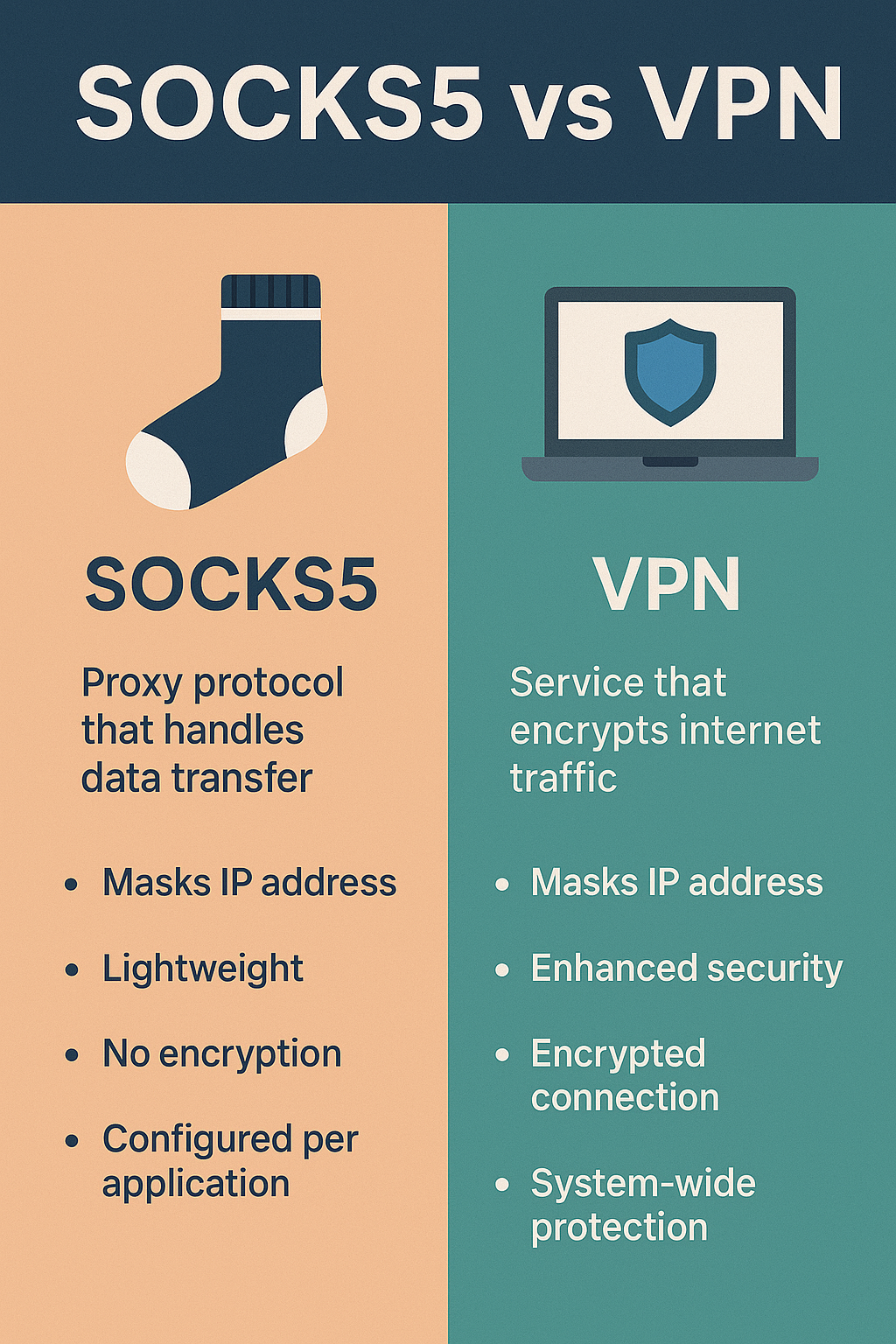
| Layer | Scope | Strengths | Trade-offs |
|---|---|---|---|
| SOCKS5 | Per application | Precise routing, simple firewall rules, UDP via associate | No native encryption — pair with TLS or VPN for confidentiality |
| VPN | System or user session | Single trusted encrypted pipe, easy adapter binding | All-or-nothing unless split tunneling is carefully configured |
| HTTPS proxy | HTTP/HTTPS only | Easy browser integration, can add caching or content policy | Protocol-specific — not designed for arbitrary TCP or UDP |
Best combination for torrenting: SOCKS5 in qBittorrent for per-app routing + system VPN for confidentiality + firewall deny-outside-path. See the qBittorrent setup guide for full steps.
⚙ Safe configuration patterns
1
Bind the app to the proxy path
Set SOCKS5 host, port, and authentication in the app. Confirm that direct egress is disabled — most clients have a checkbox for "use proxy for all connections".
2
Decide on encryption
If data needs confidentiality, pair SOCKS5 with TLS inside the app or run the app inside a system VPN. For torrenting, the swarm traffic itself doesn't require encryption — IP masking is the goal.
3
DNS policy
Route name lookups through the same trusted path as the app traffic. For qBittorrent, enable "Perform hostname lookup via proxy" in the Connection settings.
4
IPv6 stance
Permit or disable IPv6 for the app explicitly. Avoid mixed states — an app that routes IPv4 through the proxy but resolves IPv6 directly has a side channel.
5
Firewall deny by default
Allow the app to reach the proxy. Deny the app to reach any other external address. This creates the fail-closed guarantee that protects you even if the proxy disconnects.
🔬 Validation: test then monitor

1
Run a free torrent IP check — confirm the swarm sees your proxy IP, not your real one
2
Check DNS queries follow the same trusted path — not falling back to other resolvers after reboot
3
Monitor logs for adapter changes, resolver flips, and unexpected ports — especially after OS updates
FAQ Common questions
Is SOCKS5 the same as encryption?
No. SOCKS5 is a relay and routing mechanism — it hides your IP from destinations but doesn't encrypt the payload. Add TLS inside the application or use a system VPN when confidentiality is required.
When should I choose SOCKS5 over a VPN?
Choose SOCKS5 when you want per-application routing and precise egress control — especially for torrenting where you want the client isolated without routing all your traffic through the tunnel. Choose a VPN when you need a single encrypted path for the entire system.
Can SOCKS5 handle UDP traffic?
Yes, via the UDP ASSOCIATE command. Application support varies — qBittorrent supports it. Test your specific use case, and note that some firewall configurations block UDP associate by default.
Key takeaways
✓
SOCKS5 gives per-app routing and clean firewall policy. It hides your IP but does not encrypt by itself.
✓
Pair with TLS or a system VPN when confidentiality is needed alongside IP masking.
✓
Keep DNS and IPv6 policy consistent with the app route — verify after reboots and adapter changes.
See SOCKS5 in action
Free torrent IP check — no signup
Verify the proxy is actually routing your torrent traffic. Check what IP the swarm sees in 30 seconds.
