The Future of Torrent Privacy (2025–2028):
What's Changing and How to Stay Ahead
Torrent privacy isn't static. In 2025 and beyond, users will juggle performance, convenience, and policy pressure while networks grow smarter. This article looks ahead — what remains effective, what's changing, and what's emerging — with realistic projections and takeaways you can apply today whether you're on a desktop, a seedbox, or a headless NAS.

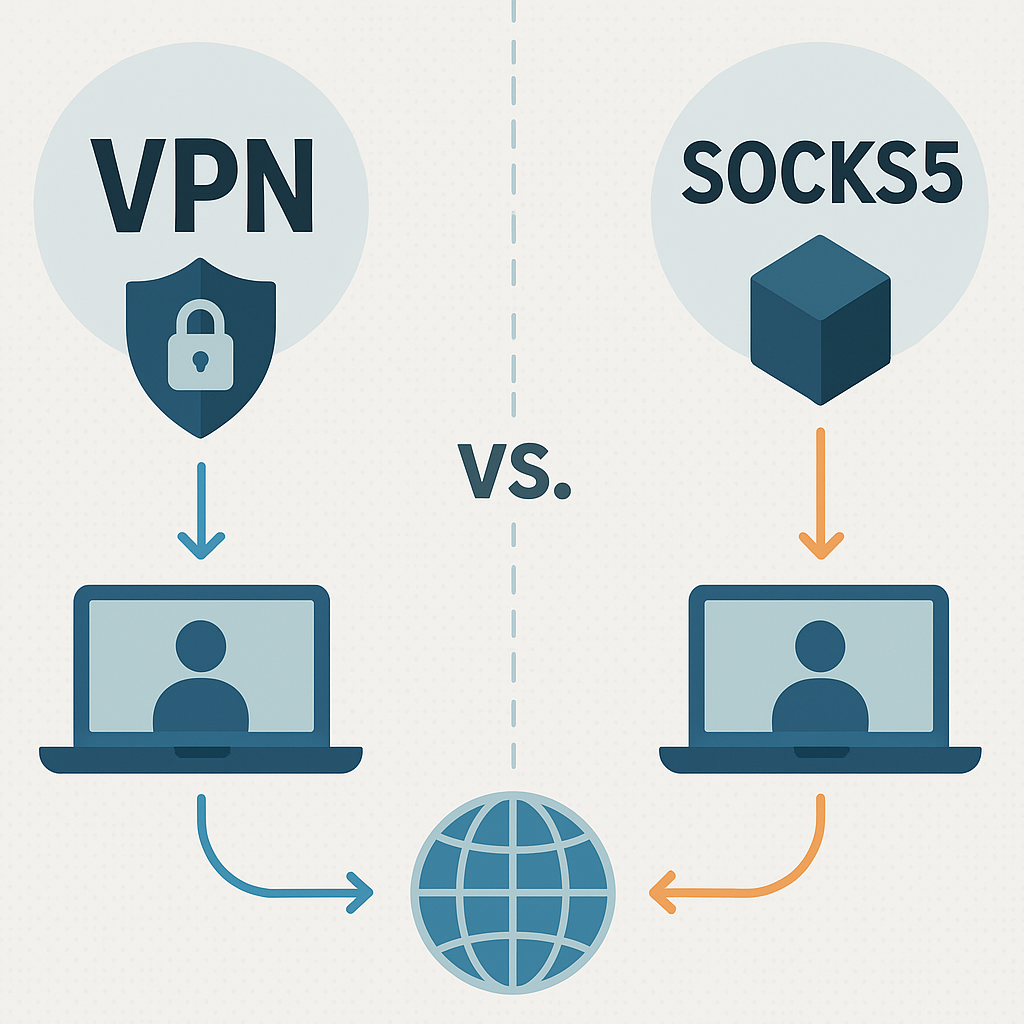
📍 Where we are now: VPNs and SOCKS5 still matter
VPNs remain the baseline privacy layer for torrent users — a single encrypted egress path that's easy to reason about. SOCKS5 proxies are efficient and flexible: no native encryption, but many users combine them with system-level encryption, or use SOCKS5 primarily to isolate the app route and simplify firewall rules.
📡 Three forces reshaping torrent privacy
🔭 2025–2028 projections
These are directional — use them to guide choices that age well, not as certainties.
| Area | Projection | What to do |
|---|---|---|
| Traffic classification | More edge-side heuristics; pattern-based throttling or disruptions | Prefer stable ports; keep encryption on; consider traffic shaping to avoid signature spikes |
| DNS measures | Region-specific resolver policies and short-lived blocks | Use a resolver you trust; verify after restarts; maintain alternative resolution paths |
| Client defaults | Safer defaults for binding, DHT/PEX rules, and startup checks | Audit your client after upgrades — updates sometimes reset settings |
| Seedboxes and headless | Greater adoption; more web UIs; more reverse proxies | Lock down auth; IP allowlists; rate limits; TLS; no open UI exposure |
| Decentralized relays | Early practical options will appear — mesh/relay networks, programmable egress | Evaluate on small torrents first; inspect logs, routes, and failure modes carefully |
⚖ VPNs vs SOCKS5 vs decentralized relays
| Layer | Strengths | Trade-offs | Best fit |
|---|---|---|---|
| VPN | Simple model; full-tunnel option; easy to firewall | All-or-nothing; split tunneling must be managed carefully | Desktops and laptops — one trusted pipe for everything |
| SOCKS5 | Per-app routing; lightweight; container and seedbox-friendly | No native encryption — pair with TLS or OS/VPN | Headless, NAS, multi-service hosts with granular policy |
| Decentralized relays | Path diversity; resilience; potentially community-governed | Early-stage UX; variable reliability; needs careful routing | Power users who can test and validate new routing layers |
🌐 Decentralized and programmable privacy: what it might look like
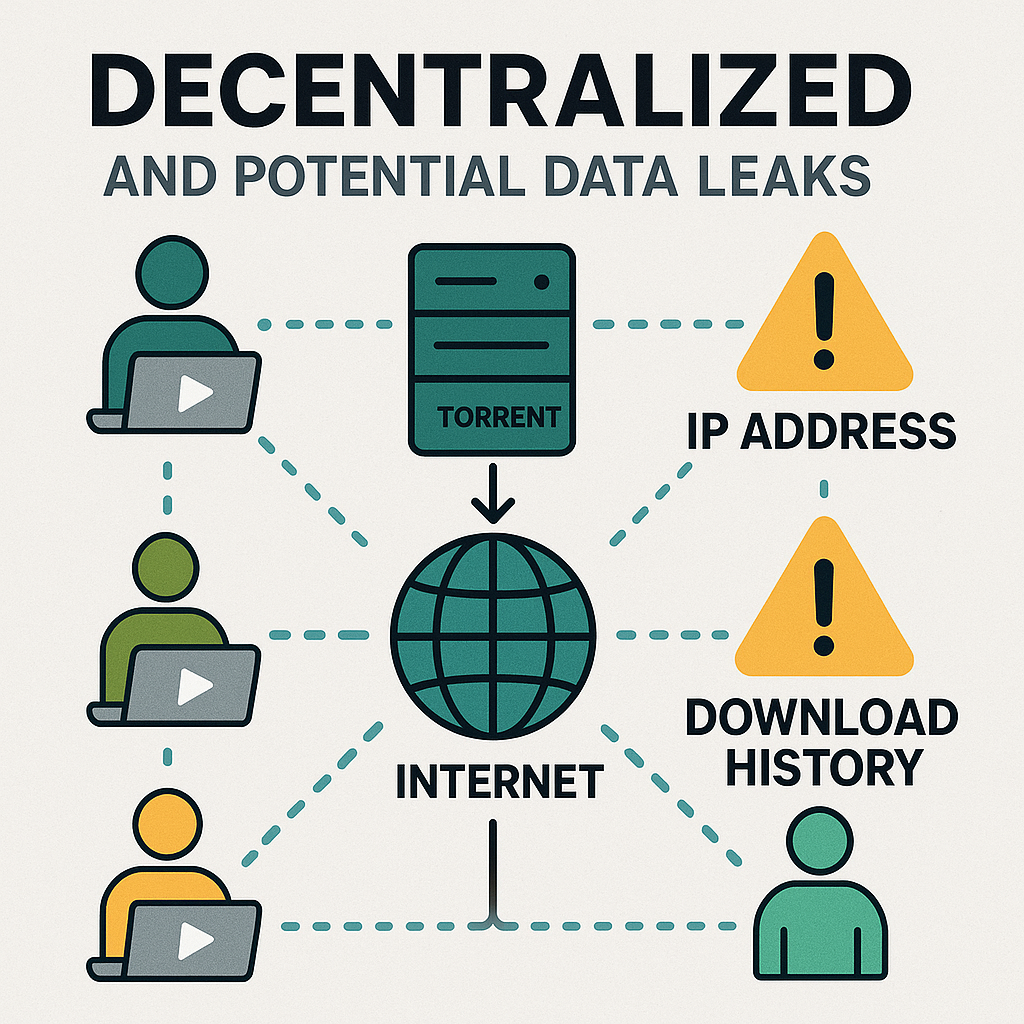
Imagine a privacy layer that feels like a VPN from your torrent client's perspective, but under the hood uses programmable relays. A controller chooses egress nodes based on live conditions — latency, reputation, geography — and policy: no open UI exposure, DHT scope rules, deny if DNS flips. A user could pin a region, cap latency, and assert that any adapter change halts the client until checks pass.
🔧 Operational hygiene that will still matter in 2028
📖 Quick scenario playbook (2025–2028)
🖥 Home desktop
🖧 NAS / headless server
🌱 Seedbox
⚗ Power user (experimental)
Advanced
FAQ Frequently asked questions
Will VPNs become obsolete?
Is SOCKS5 enough on its own?
How would decentralized relays help?
Free torrent IP check — no signup
Whatever the future brings, confirming your proxy is routing traffic correctly takes 30 seconds and costs nothing.
